Your phone number has quietly become one of the most powerful identifiers on the internet. It connects your banking apps, social media, messaging platforms, and sometimes even your crypto accounts.
That convenience also makes it a valuable target.
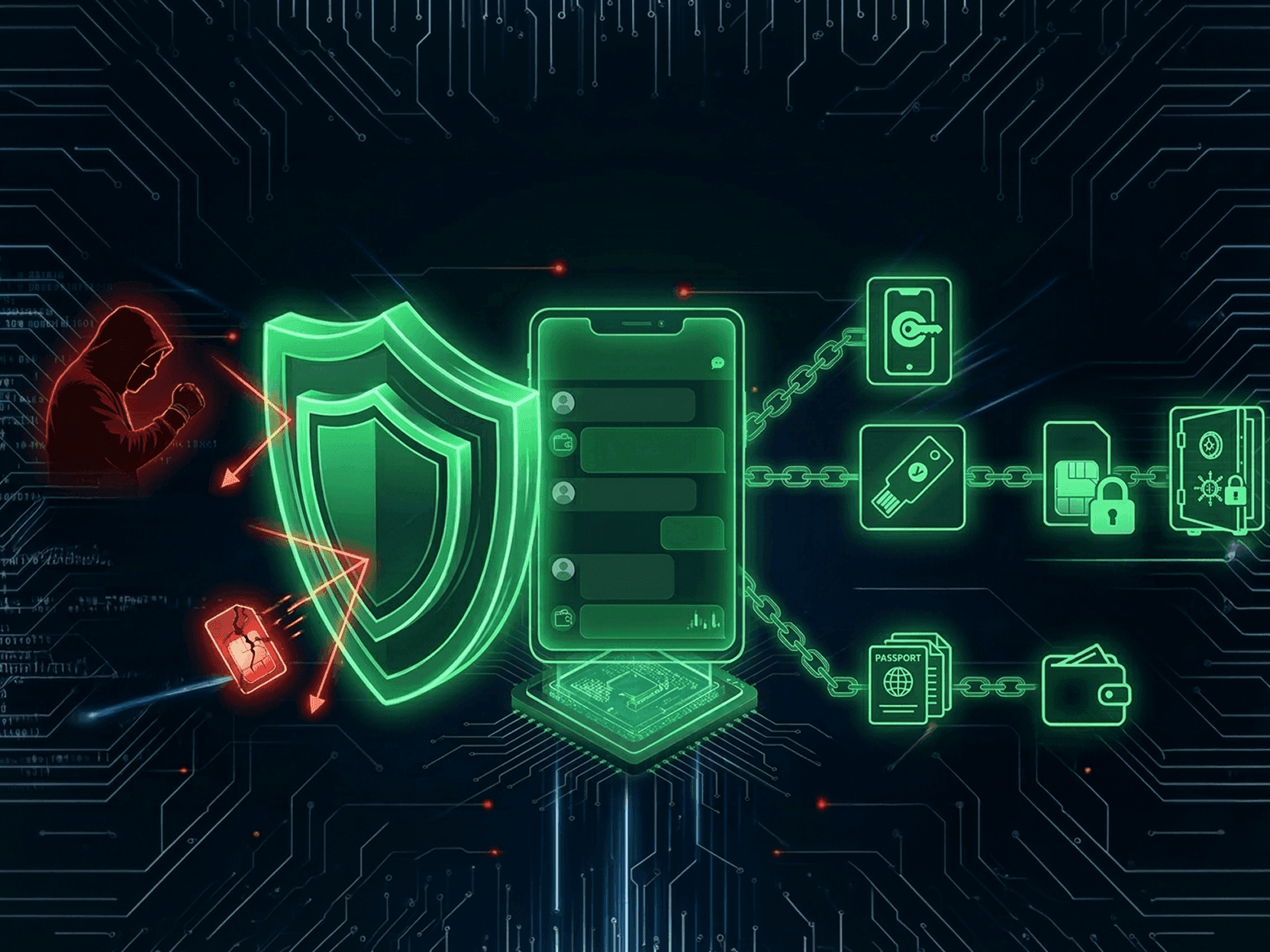
A SIM-swap attack allows a hacker to take control of your phone number by convincing a mobile carrier to transfer it to a new SIM card. Once that happens, the attacker can receive your calls, texts, and verification codes—often gaining access to accounts that rely on SMS authentication.
For messaging apps tied to phone numbers, this creates a serious security problem.
Understanding how SIM-swap attacks work—and how messaging platforms deal with them—can help you significantly reduce your risk.
What Is a SIM-Swap Attack?
A SIM-swap attack happens when someone tricks or manipulates a telecom provider into transferring your phone number to a SIM card they control.
Attackers typically gather personal data first. This may include:
leaked information from data breaches
social media details
phishing messages
compromised email accounts
Using this information, they contact the mobile carrier and impersonate you. If successful, the carrier activates your number on their SIM card.
From that moment on, they receive:
SMS verification codes
phone calls
account recovery messages
This allows them to reset passwords or bypass authentication on services connected to your number.
Crypto investors, developers, journalists, and public figures are frequent targets—but the attack can affect anyone.
Why Messaging Apps Are Vulnerable
Many messaging platforms use phone numbers as the primary identity layer. This creates several weaknesses:
1.
Account takeover via SMS verification. If an attacker controls your number, they can often re-register your messaging account.
2.
Contact discovery exposure. Apps that automatically sync contacts can reveal who you communicate with.
3.
Metadata leaks. Even if messages are encrypted, account identity may still rely on a phone number.
The more services tied to a single number, the larger the attack surface becomes.
How to Reduce the Risk of SIM-Swap Attacks
While no system is completely immune, several practical steps can significantly reduce your exposure.
1. Strengthen your mobile carrier security
Ask your provider about:
port-out protection
SIM transfer PINs
account security flags
These make it harder for attackers to transfer your number.
2. Avoid SMS-based authentication when possible
SMS verification codes are convenient but vulnerable. Where possible, switch to:
authenticator apps
hardware security keys
device-based authentication
3. Minimize the number of services tied to your phone number
If every service relies on your number, a SIM swap becomes a master key.
Reducing that dependency dramatically lowers risk.
4. Choose messaging platforms that don’t depend on phone numbers
The most effective defense is using apps where identity is not tied to real-world identifiers such as phone numbers or emails.
These platforms typically use:
cryptographic keys
peer-to-peer communication
temporary session links
This removes the SIM card as a potential attack vector.
Secure Messaging Apps and SIM-Swap Risk
Different messaging apps take very different approaches to identity and account setup.
Messenger | EXTRA SAFE | Telegram | Signal | Session | |
|---|---|---|---|---|---|
Requires Phone Number | No | Yes | Yes | Yes | No |
Anonymous Setup | Yes | No | Limited | No | Yes |
Browser/Link Chat | Yes | No | No | No | No |
Ephemeral Sessions | Yes | Limited | Optional | Limited | Yes |
Apps that depend on phone numbers can be vulnerable to SIM-swap account takeover. Platforms that rely on cryptographic identity instead of phone numbers remove that attack vector entirely.
Some modern messaging tools also allow temporary conversations via invite links, which means participants can join a secure chat or call without creating permanent accounts.
A Different Security Model
A growing category of privacy-focused messaging platforms avoids real-world identifiers entirely. Instead of signing up with a phone number or email, users connect using:
encrypted session keys
temporary invite links
peer-to-peer connections
This model prevents attackers from hijacking an account simply by taking control of a phone number.
For example, EXTRA SAFE allows users to start encrypted conversations without registering personal identifiers. Chats and calls can be created directly inside the app or launched via secure invite links, enabling temporary and identity-free communication sessions.
This approach dramatically reduces the role of telecom infrastructure in communication security.
Why This Matters for Secure Communication
SIM-swap attacks highlight a broader security lesson: when identity depends on centralized systems like phone numbers, those systems become the weakest link.
By reducing reliance on phone numbers, SMS verification, and permanent accounts, modern secure messaging platforms can eliminate entire classes of attacks.
For users who regularly share sensitive information—whether personal, financial, or professional—choosing a messaging platform with anonymous setup and cryptographic identity is one of the most effective steps toward protecting communication privacy.
Take Control of Your Communication Security
SIM-swap attacks exploit a simple weakness: when your communication identity depends on a phone number, anyone who gains control of that number can potentially gain control of your accounts.
The safest approach is to reduce that dependency entirely.
Using messaging platforms that don’t rely on phone numbers or emails and instead operate through cryptographic identities and peer-to-peer connections, removes the SIM card from the security equation. It also allows conversations to happen without exposing personal identifiers or creating permanent communication records.
If you want to protect your conversations from SIM-swap risks and similar identity-based attacks, consider using EXTRA SAFE. It allows you to start encrypted chats or calls without registration, share temporary invite links for private conversations, and communicate without tying your identity to a phone number or email.
Try EXTRA SAFE and experience private communication without identity exposure.